Memorandum
Subject: Human Weakness
To: All Readers and Interested Parties
From: Greg Smith, Author
Date: 6 MAR 2026
BACKGROUND:
History is replete with human conflict. Territorial disputes, vanquishing new lands, enslaving neighbors, lust for gold and other treasures drive the desire for conquest. In many conflicts, the victor is determined by having a larger army, better weapons, or more skilled battlefield leaders. In other cases, the winner is determined through subterfuge, deception, traitors, or espionage. There are innumerable reasons why someone decides to serve an enemy, including financial gain, ideology, coercion, or simply excitement.

At the battle of Thermopylae in 480 BCE, a force of around 6000 Greeks, anchored by the famed 300 Spartans, held off the Persian Army of Xerxes for three days. Although the Persians outnumbered the Greeks by a factor of at least 25:1, the Spartan King, Leonidas, placed the Greek forces in a highly defensible position blocking the narrow pass. By the second day, Xerxes had lost an estimated 20,000 soldiers with no appreciable gain. The battle was won only after a Greek traitor seeking financial reward led the Persians through a lesser-known trail around the pass to attack the Greek forces from the rear.

During The American War for Independence (1775 – 1783), Benedict Arnold, a highly-regarded battlefield leader and hero of the victory at Fort Ticonderoga, oversaw the defense of West Point, a strategic passage along the Hudson River. Having been denied promotions and recognition by the Continental Congress, he decided to betray the cause. He willingly provided the British with the defense plans and other vital intelligence in exchange for a commission as a Brigadier General in the British Army. Arnold later led British forces in the sacking and burning of New London, Connecticut, in 1781.

World War I (1914 – 1918), saw the rise of communism and the downfall of several great empires. The ideals of communism saw the rise of the Soviet Union and the widespread acceptance of communist principles. Many saw communism as a utopian form of governance, where all people shared resources and output equally. During the Great Depression (1929 – 1935), these ideas saw widespread acceptance, particularly on university campuses in Europe. At Cambridge University in England, the NKVD, a predecessor of the infamous KGB, recruited five students who became among the most prolific and effective spies in modern history. All five had links to British aristocracy or access to military and political secrets. The five men, Kim Philby, Guy Burgess, Donald Maclean, Anthony Blunt, and John Cairncross passed sensitive information to their Soviet handlers throughout World War II and into the atomic age, including nuclear secrets. Their activities lasted through the 1950’s. Three of the five would eventually defect to the Soviet Union to escape capture.

John Vassal was a British civil servant in the Admiralty, assigned to the British Embassy in Moscow in 1955. The Soviet KGB discovered that Vassal was a closeted homosexual. During a social event, the KGB used drugs and alcohol to lower his inhibitions and photographed him engaged in sexual activity with other men. The KGB used these photographs to blackmail Vassal into passing secrets to the Soviets. Following his return to England, Vassal was assigned to the intelligence section at the Admiralty and the KGB continued to exploit him. This continued until KGB defectors alerted the British to Vassal in 1962.

During the 1980’s and 1990’s, the United States was rocked by a series of espionage scandals. A US Navy communications specialist named John Walker recruited his son and colleagues into helping him pass highly sensitive information concerning US nuclear submarines to the Soviets for money. Aldrich Ames, a CIA analyst, passed details of ongoing CIA activities and double agents to the Soviets in exchange for money. During the same period, Robert Hanssen, the head of the FBI counterintelligence division, was also passing secrets to the Soviets. In the Defense Intelligence Agency (DIA), Ana Montes was considered the expert on Cuba. Unbeknownst to her colleagues, she was also passing secrets to Cuban intelligence. In all these cases, US national security was jeopardized.
Intelligence gathering and espionage is not limited to activities involving adversary nations. Allies also spy on each other for various reasons. Not all information or key technological advancement is shared between friends. Allies may seek to understand the internal decision-making process of the leaders to determine where to press for advantage. One of the more famous cases of such espionage involved Jonathan Pollard. In the 1980’s, Pollard was an intelligence analyst at the Naval Intelligence Command. He offered his services to several countries, including Israel. He pled guilty in 1986 and was released from prison in 2015. In 2020, he emigrated to Israel where he obtained full citizenship.

In all these cases, human weakness, ideologies, and desires led to massive security failures. In the case of Alrich Ames, at least ten highly placed agents were killed because of his betrayal. No matter how secure or highly classified information is, there is always a risk of exposure. Prior to most overseas assignments, service members, politicians, and civil servants all receive detailed anti-terrorism briefings and training. Some of that training is required to be accomplished annually or at least on a regular basis. In the intelligence field, regular polygraph exams are commonplace but are not infallible as shown in the cases of Ames, Hanssen, and Montes, all of whom passed numerous such exams while actively engaged in espionage activities.
John Walker agreed to plead guilty in exchange for a reduced sentence for his son Michael in 1987. He died in prison in 2014. Robert Hanssen pled guilty to 13 counts of espionage to avoid the death penalty. He died in prison in 2023. Aldrich Ames pled guilty to espionage and tax evasion in 1994. He was sentenced to life in prison and died in January 2026. Ana Montes accepted a plea agreement to avoid a possible death penalty. She was sentenced to 25 years in prison. She was released in 2023, and resides in Puerto Rico, where she continues to speak out against the US policy toward Cuba. While incarcerated, Montes wrote to a friend that the “morality of espionage” is relative.
INTELLIGENCE ASSESSMENTS:
In some ways, Montes was correct in stating that the morality of espionage is relative. To those who are ideologically driven, like she was, actively working to undermine their country is both right and morally proper. Similarly, the Cambridge Five also saw their work on behalf of the Soviet Union as morally justified. Initially, they rationalized passing secrets to the Soviets as working to aid an ally during the war against Hitler. They continued passing secrets after the war in the belief that doing so would preserve peace and prevent the temptation to use nuclear dominance to exert power.
Espionage relies on exploiting human weaknesses. Although a great deal of espionage and intelligence gathering is now done electronically, it is only through personal contact that some insights are gained. Potential adversaries seek to recruit, coerce, or purchase the services of those with access to needed information. Intelligence services seek to place trained sources near those with access to desired information. Politicians have been a common target of such practices. In recent years, several US congresspeople have been compromised to varying degrees by Chinese agents. One California senator unknowingly employed a Chinese agent as her driver for nearly twenty years. Another senator carried on a personal relationship with an attractive female agent whom he met while she was working on his campaign. Both politicians were members of key Congressional committees.
China probably has the most active human intelligence gathering system working today. Chinese agents, sleepers, and proxies flood the US and western countries to sway public opinion, solicit or steal information, and gain access to the halls of power. China also takes a long view of their activities, sometimes placing sources near targets whom they expect to see in higher positions in the future. Sometimes, Chinese agents even work to help the targeted official achieve the desired roles. In 2025, a campaign advisor in San Bernadino, California, was arrested for serving as a foreign agent.
Nearly every week there is another foreign agent identified, arrested, or charged by the FBI. Chinese PhD students were arrested in in June and November 2025 for importing toxic biological substances, altered seeds, and chemicals into the US. The seeds and chemicals were both shipped from China and concealed in luggage and personal items like toothpaste tubes, possibly intended for agro-terrorism. In Las Vegas, a house located very close to Nellis Air Force Base was found to contain an illegal biolab. More than 1000 samples of toxic substances were discovered, along with an active laboratory in the garage. The owner has been linked to the Chinese Communist Party (CCP) and has been in prison since his arrest in 2023 following the investigation at another house with a similar lab he owned in Reedley, California.
Other known espionage targets include defense contractors and high technology firms. Chinese employees in both sectors have been arrested, tried, and fled the US to avoid prosecution. A Chinese employee at Google was arrested in January of 2026 for stealing secrets related to Artificial Intelligence and AI products. The CCP also established a “secret” police station in New York and possibly other cities to both spy on their own people and to influence the activities of others. The Center for Strategic & International Studies (CSIS) cites over 200 cases of Chinese espionage and over 1200 cases of industrial espionage targeting the US since 2000.
Espionage is not limited to theft of secrets. In some cases, the CCP recruited, coerced, or paid Chinese nationals and those of Chinese descent to act as agents. The CCP tasked the individuals to follow Chinese dissidents and report on their movements. There have been reports of Chinese Americans who were paid to follow Taiwanese delegations and report on movements, as well as following the acrobatic dance group Shen-Yun, due to their links to the Falun-Gong spiritual movement the CCP considers a threat to the state. In February 2025, the Australian Prime Minister was threatened with a bombing unless the dance group performance was cancelled.

China is known to employ both bribery and intimidation tactics against individuals residing in the west. Even the 2026 Olympics Champion, Alysa Liu and her father Arthur were targeted by Chinese agents. In their case, Chinese agents, pretending to be representatives of the International Olympic Committee, solicited personal information. As an outspoken critic of China, Mr. Liu became suspicious and reported the attempt. Such intimidation tactics are common with Chinese nationals and refugees residing in western countries, particularly if they have extended family remaining in mainland China.
In other cases, China uses money to obtain information, sway potentially unfavorable opinion, or gain social media influencers. The CCP is willing to spend lavishly to gain knowledge through willing (or unwitting) collaborators. A retired US Air Force fighter pilot was arrested by the FBI in February 2026 for arranging the combat training of Chinese military pilots. The American pilot, a former instructor in the F-15, F-16, and F-35 programs, possessed information about US tactics, aircraft capabilities and vulnerabilities, and the combat training of US pilots.
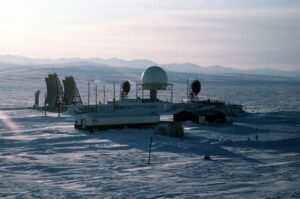
Most espionage today relies on electronic means. Spy satellites have been the primary intelligence gathering system in the US since the 1970’s. In 1979, following years of negative stories related to CIA activities around the world, Stansfield Turner was appointed the Director of Central Intelligence and given the mandate to clean up the agency. He eliminated over 800 operational positions. Field operations and the collection of intelligence from people in targeted countries were severely curtailed in favor of electronic surveillance and collection. The recruitment and management of willing spies, cultivation of sources, and conduct of field operations in targeted countries effectively ended. In the absence of human exploitation, other agencies, like the National Security Agency (NSA) and National Geospatial-Intelligence Agency (NGIA) took on the responsibility for electronic and remote intelligence gathering.
Espionage and intelligence gathering are vital and misunderstood aspects of national security. For many people, their understanding of such activities are either based on James Bond or Jason Bourne movies, Jack Higgins and John LeCarre novels, or other works of complete fiction. Espionage and intelligence rely on gathering many bits of knowledge and stringing them together to form a coherent picture. With the advent of AI, intelligence gathering and exploitation requires fewer people. In a recent case, a hacker trying to reprogram a robot vacuum gained access to thousands of such devices, including their cameras and internal mapping capability. Virtually every home, office and government facility is full of similar vulnerabilities from cameras, televisions, computers, cell phones, video conferencing equipment, “smart” plugs, and even appliances. What vulnerabilities could an enemy exploit in a potential conflict because of our reliance on technology?
CURRENT OPERATIONS UPDATE:
The latest rewrite and update to Killer’s Reign is complete. The novel has been through two rounds of story edits and is a much stronger story. Still, there is a lot left to do to get it ready for publication. I have been slowed recently due to ongoing renovations at the house, and a pair of compressed discs in my back that have been far more painful than I would have expected. Meanwhile, I continue to work the rewrite of Sleeper Cell and develop the plot and story line for a World War II historical fiction thriller and associated screenplay.
COMMUNICATIONS UPDATE:
There is never a shortage of story ideas, truth is stranger than fiction. Every news cycle is full of conflicts, tragedy, intrigue, and treachery. Every event sparks ideas for a story. My stories, Killer’s Reign and Sleeper Cell draw on current events as well as my own experience. Likewise, my planned historical novel relies on real people fighting behind the lines in occupied France and Italy during World War II. Although I write works of fiction, I strive to ensure that the events and characters are plausible and representative of real word events and scenarios.
Check my website regularly for more information about my books and stories, updates on current events, links to other works, and interesting tidbits of intelligence.
https://gregsmithonline.com/
www.linkedin.com/in/gregmsmith17
Stay Alert. Stay Informed. Stay Aware.
Greg Smith
Author
cc:
S2 Intelligence
S3/5 Operations & Plans
S6 Communications